Cyberwar: Use of Flame virus to deter Iran 'reasonable', says Israel
Minister comments on use of cyber weapons, such as a virus, to counter Iran's nuclear plans.
"For anyone who sees the Iranian threat as significant, it is reasonable that he would take different steps, including these, in order to hobble it," Vice Prime Minister Moshe Yaalon told army radio, just hours after the virus was discovered by Russia's Kaspersky Lab.
"Israel is blessed with being a country which is technologically rich, and these tools open up all sorts of possibilities for us," said Yaalon, who is also Israel's strategic affairs minister.
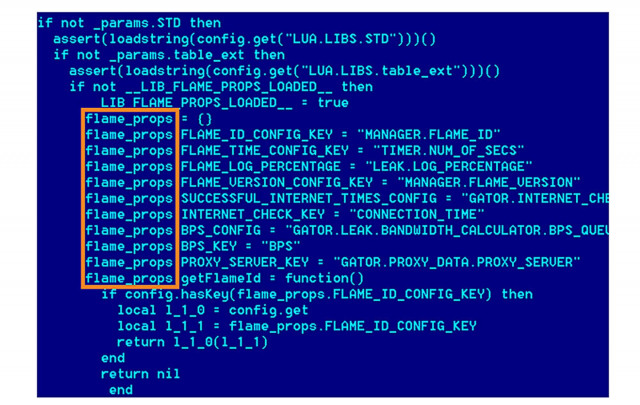
Kaspersky Lab, one of the world's biggest producers of anti-virus software, said its experts discovered the virus -- known as Flame -- during an investigation prompted by the International Telecommunication Union (ITU).
Iran appears to have been the main target of the attack, and the announcement comes just a month after the Islamic republic said it halted the spread of a data-deleting virus targeting computer servers in its oil sector.
It said the virus was "about 20 times larger than Stuxnet," the worm which was discovered in June 2010 and used against the Iranian nuclear programme, with Israel widely suspected of involvement.
Israeli Prime Minister Benjamin Netanyahu, while not mentioning Flame, spoke on Tuesday of Israel's cyber prowess.
"In the cyber arena, the size of a country is not that important but there is great significance in its scientific ability and in that Israel is blessed," he told an international security conference at Tel Aviv University.
"We are investing huge capital in that; human capital and financial capital, and I expect that investment to grow in the coming years. I have set the target of Israel being among the five leading world powers in the cyber field."
A Kaspersky statement said Flame is "actively being used as a cyber weapon attacking entities in several countries," describing its purpose as "cyber espionage."
"The complexity and functionality of the newly discovered malicious programme exceed those of all other cyber menaces known to date," it added.
"It's like nothing else we've seen before," said Ilan Froimovitch, chief technical officer of Kaspersky's Israeli representative, Power Communication.
"It's like they took the best from every malicious code there is and combined it into one code."
He said that the originator of the programme was most probably a state or a coalition of states.
"It is not likely that an individual or even a private company would invest so much effort and so much time and money," he said. "This must be the work of a government or a few of them.
"I don't think that this is a 16-year-old nerd that is trying to sit and write some code and do some damage," he added. "It is not designed to do damage, it is designed to gather intelligence, it is designed to be unknown."
Froimovitch declined to say if he thought Israel was capable of such a project.
"We have great knowledge in Israel and we like to think that we are the smartest in the world, but evidence shows that there are probably a few more countries in the West that can work like that."
Alexander Gostev, Kaspersky's chief security expert, said Iran was the country by far the worst affected by Flame, followed by Israel and the Palestinian Territories, Sudan, Syria and Lebanon.
"The geography of the targets and also the complexity of the threat leaves no doubt about it being a nation state that sponsored the research that went into it," he said in an analysis article.
He said the aim of the virus was clearly to "collect information" on the operations of states in the Middle East such as Iran, Lebanon and Syria.
According to Western media reports, Flame has been used to attack the Iranian oil ministry and Iran's main oil export terminal.
Kaspersky said Flame had been "in the wild" for more than two years, since March 2010.



















COMMENTS
Comments are moderated and generally will be posted if they are on-topic and not abusive.
For more information, please see our Comments FAQ