Incoming mail.
No, it’s not an irate writer demanding why their byline hasn’t appeared on a story. It’s something completely unexpected. It’s a follow-up comment to a post by Asif criticizing me for slamming his article on an independent blogging site.
The only problem is, I have no idea who Asif is and have not read his blog post or visited the site in question.
I head over to the link provided - the email is one of those auto-responses to a blog post whose comments you wish to follow.
I read Asif’s piece, and then I scroll down to the comments section. This is what I find:
Jay Hacker says:
July 13, 2010 at 2:59 am
Unemployed writers will always have narrow view points
Keep in mind that I often write under the pseudonym Jay Haque. Not only has Jay Hacker used my email address, they have also put in tribune.com.pk as the user's URL. Very legit.
Assuming this is actually me, Asif responds:
Asif says:
July 13, 2010 at 4:22 am
Neither am I a writer nor am I unemployed. The purpose of this article was to introduce the growing discipline of political marketing the issues discussed in the blog are simply laying the foundations of this still developing discipline. My aim was simply to encourage some debate.
However as “journalist” (I’ve read your work) working for the Tribune I don’t know how you could miss this point. A little tip from an “unemployed writer” is to not always use the same angry man approach to every article it gets boring after a while or may be this is simply an approach to look more superior to the rest of the people who manage stumble upon your writing.
I’m appalled, but not overly so. It’s easy to disguise an identity online, and even easier to pose as another individual. In the initial days of setting up tribune.com.pk the web team had a long debate over this very same issue with regards to our comments section.
How would we ever know if someone filling out their name and email address wasn't lying?
How would we prevent identity theft and individuals commenting on stories with an assumed name, possibly to undermine the viewpoint of the name they had assumed?
The team suggested multiple ways of preventing this from happening. Unique logins, password-based logins, mandatory email address verification… the list was endless, but here’s the thing: any system built by humans is just as easily hacked by humans.
Based on this, we went for a liberal policy with comments, opting for ease of dialogue for the majority over the very few cases of misuse by a vicious minority.
However, a vicious minority does exist.
I left Asif this message explaining the issue on his blog post:
Jahanzaib Haque says:
July 13, 2010 at 4:29 am
Hi Asif,
It seems somebody is impersonating me and leaving comments on blogs. Ironically, they are using my real email address so I am informed every time they leave a post on someone’s blog. Hope that clears up the confusion; also, if you are interested in blogging for us, please do email me a submission to blog@tribune.com.pk – having written for Aurora, many-a-time I wanted to do just this piece on political advertising!
Regards,
Jahanzaib
And that is really the best I can do. If someone wishes to malign my name, kudos to them; I can only consider it a form of compliment. For everyone else, always keep in mind that identity theft online is a reality, so before you proceed to bash someone for their views, make sure that person is actually who they say they are.
Or just don’t bash.
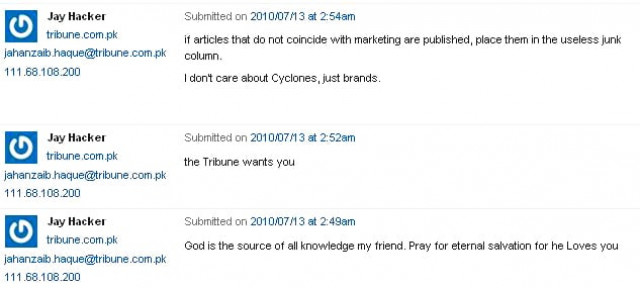
UPDATE: Blog post on Triple Bottom-line Magazine received yet another comment by Jay Hacker.
UPDATE: The hacker's IP address has revealed the individuals location to be Karachi, Pakistan using Domain Name - 10.PERN.PK. Investigation underway, IP tracked to szabist.edu.pk


COMMENTS
Comments are moderated and generally will be posted if they are on-topic and not abusive.
For more information, please see our Comments FAQ